
What makes the Data Science improvements for Cybersecurity remarkable?
Companies across the globe are trying to make the most out of data science advancements. They are also successful in creating data-driven ecosystems and obtaining valuable business insights through data science, which yields tangible benefits. Standout technologies like the Internet of Things, Artificial Intelligence, Machine Learning, and Robotic Process Automation create a complex integrated network. This may lead to a potential threat, cyber-attack.
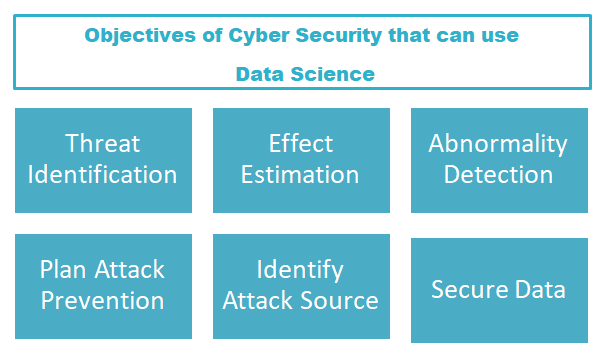
Here comes the use of recent data science application in cybersecurity. Wonder how data science could improve cybersecurity? Let’s see how big data and cybersecurity can be linked.
Companies collect data from various available sources, analyze the information using several Machine Learning tools and data analytics techniques. The results that include trends and patterns provide decision-makers with valuable and actionable insights.
Organizations can collect the data associated with network attacks, like frequency, probability and time of the event occurrence. Such information can be processed through data analytics to identify possible cyber-attack. Such information gathered can be used to predict potential cyber threats. Thus, data science saves organizations from cyber-attacks.
Secure Valuable Data :
Every organization has its own confidential data to be protected, arising a need for cybersecurity. Loss of information, either internal data or the customer data is extremely dangerous ruining companies’ reputation. By practicing several security measures organization’s data can be secured. Data science can be used in scrutinizing the most targeted areas through algorithms and identifying the network most prone to attacks.
Hasten Time-Consuming Tasks :
By using data science algorithms a few time-consuming tasks in dealing with cybersecurity can be implemented faster. By processing the data, observing the patterns and trends in data, and identifying the possible source of abnormality it will reduce the need for manual effort and quicken the process. Along with ML, data science can do much more like alerting in case of new threat including internet-borne attacks.
Threat Intelligence :
Data science application in cybersecurity can be used not only to identify threat but can also be used in risk management. It provides actionable insights in managing real-time attack detection. It helps organizations to limit losses by suggesting preventive measures so that the attack doesn’t reoccur.
Organizations should make the most out of Data Science techniques for advancements in Cyber Security.
Statistical Methodology :
Data Science can be correlated to cybersecurity in planning a cyber-attack defense. By interpreting normalities through patterns in data, identification of abnormality becomes easier and faster. Organizations can process the available appropriate data through algorithms to extract adequate outcomes. Decision-makers will then be able to assess the effectiveness of the solution and will also succeed in preventing possible cyber-threat.
Predictive Analytics :
The rate of cybercrimes has been increased over time. Organizations have to process a diverse large amount of data to identify or predict cyber threats. Performing predictive analytics along with ML or AI on relevant data, companies can save their data, by reacting immediately to forecasted attacks. Through Self-learning analytics, data scientists can monitor activities across various networks in real-time to identify threats in network traffic and data flows.
To conclude, effective data science techniques empowers cybersecurity. It helps companies to develop powerful defense mechanisms against cyber-attacks. Athena helps companies to leverage data science with self-learning algorithms, creating a data-driven ecosystem. Inorder to contact us Click here

Enjoyed looking through this, very good stuff, thankyou.